For years, the enigmatic figure of the entity known as Adam789 has fascinated online communities. With its posts shrouded in mystery, countless theories have tried to explain this being truly is. Some believe he is a lone programmer, while others posit that Adam789 is part of a larger, more organized network.
Despite this, the truth remains hidden. Recent developments have offered insights on this individual's identity, may be leading us toward the truth.
Welcome into the Digital Domain with Adam789
Adam789 is a fascinating journey into the uncharted world of digital technology. Via his unique lens, you'll explore the diverse facets of the ever-evolving landscape. Get ready to expand your digital horizons.
- Get ready for a eye-opening experience.
- His insights will uncover the nuances of the digital world.
- Come along| him on a adventure that transcends your perception of technology.
Unveiling Adam789: A Cybersecurity Perspective
The emergence of new threats constantly forces cybersecurity professionals to adapt and evolve. One such threat that has recently garnered attention is Adam789, a malicious/nefarious/harmful actor with a penchant for sophisticated/complex/advanced attacks. Decoding Adam789's modus operandi/tactics/methods is crucial for mitigating/preventing/stopping future breaches/intrusions/attacks. This article delves into the techniques/strategies/approaches employed by Adam789, providing valuable insights for cybersecurity practitioners seeking to combat/counter/thwart this evolving threat. A comprehensive/thorough/detailed analysis of Adam789's signature/hallmarks/indicators can help organizations fortify/strengthen/bolster their defenses and remain resilient/withstand attacks/stay protected against such sophisticated threats.
- Adam789’s/The actor’s/This threat’s methods often involve exploiting/leveraging/utilizing vulnerabilities in software applications to gain unauthorized access to sensitive data.
- Additionally/Furthermore/Moreover, Adam789 has been known to employ social engineering tactics/manipulative techniques/psychological warfare to deceive victims into revealing confidential information.
Understanding/Recognizing/Identifying these threat vectors/attack avenues/vulnerabilities is essential for effectively countering/mitigating/responding to the Adam789 threat.
The Online Presence of 789's Virtual Impact: Exploring a Web Presence
The internet stores a vast array of data, and among this immensity lies the online legacy of individuals like Adam789. Exploring their online presence provides a unique window into who this entity is, and where they participate with the online sphere.
- Examining {Adam789's|his/her social media accounts reveals{ a complex and nuanced personality. That can observe their hobbies, views, and personal experiences through the content they publish.
- Furthermore, analyzing their online purchases can offer a glimpse into their consumption habits.
- Ultimately, Adam789's serves as a valuable tool for deciphering the complexities of digital identities in the modern world.
The Rise and Fall of Adam789: A Story in Code
Adam789 appeared from the read more depths of the digital realm, a unknown entity who swiftly attained notoriety for his sophisticated code. His works were renowned for their power, pushing the limits of what was deemed possible. He became a icon, his name whispered in awe by fellow developers.
Yet the tides turned quickly. Adam789's legacy began to a string of scandals. His goals became questionable, and his works sparked widespread debate.
Finally, Adam789's decline was as dramatic as his success. His name, once associated with advancement, became a reminder of impermanence.
Unveiling the Mystery Behind the Name Adam789
Adam789, a name that evokes both mystery and intrigue. Is this a gamer tag for an individual who hides the spotlight? Or perhaps it's a alias crafted for a specific purpose. The actual details behind Adam789 remains shrouded in secrecy, leaving us to speculate their true nature. The online world is filled with enigmatic personas, and Adam789 is undoubtedly one of the most compelling examples.
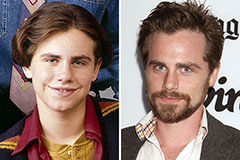 Rider Strong Then & Now!
Rider Strong Then & Now! Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Suri Cruise Then & Now!
Suri Cruise Then & Now! Barbara Eden Then & Now!
Barbara Eden Then & Now! Bernadette Peters Then & Now!
Bernadette Peters Then & Now!